Greetings Committers.
An interesting new vulnerability has been disclosed that you should know about. This vulnerability potentially impacts everybody who is involved in reviewing and accepting contributions. AFAIK, this has not actually been exploited in the wild, but it's getting enough press that it's probably only a matter of time.
The gist is that there is some potential that merge/review/pull requests may render a contribution visually in a manner that is different from how it is read by the compiler. That is, what you see on the screen is potentially different from what the compiler sees.
The researchers who discovered this vulnerability, recorded as
CVE-2021-42574, have set up a
website. To exploit this vulnerability, an attacker can leverage the Unicode characters used to enable bidirectional text in comments and strings to reorder source code characters in a way that changes its logic.
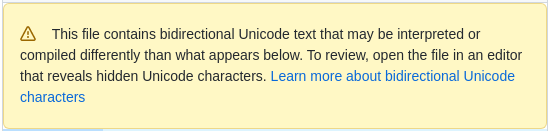
GitHub provides a warning. You'll see something like the following when you look at a file that contains any bidirectional Unicode text (including legitimate uses of bidirectional text).
I'm not sure at this time whether or not our GitLab or Gerrit provide similar warnings.
The corresponding paper describes a related issue with the use of homoglyphs to create identifiers that are visually similar but distinct to the compiler. One means of exploiting this is to create a method or function with a name and signature that is visibly exactly the same as another.
Project teams that produce software development tools: please explore options for helping our users mitigate against this risk. I'll follow up with you separately.
Let's all be careful out there.
Wayne
--
Wayne Beaton
Director of Open Source Projects | Eclipse Foundation